Insight Sphere Start 508-231-4666 Guiding Trusted Phone Discovery
The Insight Sphere approach to guiding trusted phone discovery emphasizes consistent, verifiable patterns over intuition. It relies on built-in identity tools, transparent logs, and corroborated context to affirm legitimacy. Red flags include unsolicited urgency or attempts to bypass checks. A structured daily verification routine standardizes timing cues and reinforces autonomy. When verification succeeds, intent becomes clearer; when it fails, caution rises, shaping more informed, responsible engagement and leaving questions that warrant further exploration.
How to Identify Trusted Callers: Core Principles
Identifying trusted callers relies on consistent signals rather than isolated impressions. The core principle centers on evaluating a trusted contact through verifiable patterns, not anecdotes. Verification methods include cross-checks with authoritative sources, verified caller IDs, and corroborated context. Criteria emphasize reliability, transparency, and accountability. Compelling topics emerge when indicators align with predictable behavior, enabling freedom to engage while minimizing risk.
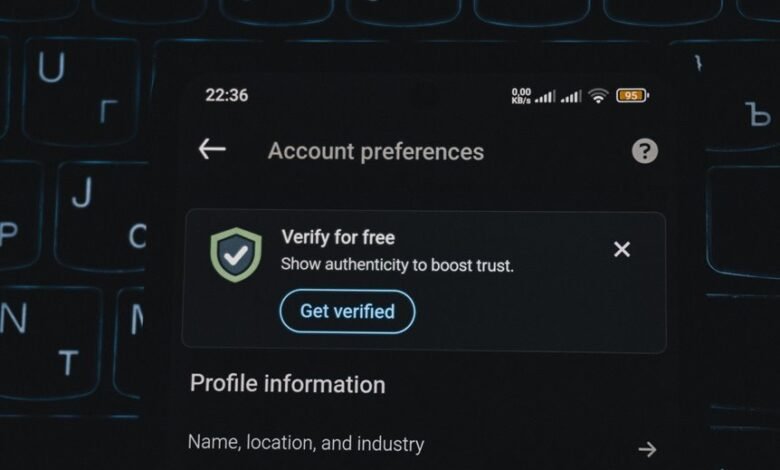
Verifying Caller Legitimacy With Built-In Tools
The analysis emphasizes how to verify caller identity through platform features, logs, and metadata, not intuition.
By using call screening and integrated verification interfaces, users gain transparent indications of authenticity.
This approach favors freedom, minimizes ambiguity, and supports deliberate, independent decision-making in communications.
Recognizing Red Flags That Signal Scams
Red flags in scam detection arise when patterns deviate from standard communication norms: unsolicited urgent requests, pressure to bypass verification, or offers that appear too good to be true.
The analysis notes discouraging pressure as a hallmark and emphasizes verifying signals rather than assumptions.
Recognizing scams relies on methodical assessment, conserving autonomy, and requiring confirming identity through verifiable channels before action or disclosure.
Establishing a Daily Voice-Call Verification Routine
Daily voice-call verification routines establish a disciplined method for confirming caller legitimacy and intent. The practice emphasizes trusted verification and consistent procedures, reducing uncertainty in daily interactions. A standardized process screens caller identity through documented checks, timing patterns, and corroborating signals. When trusted verification succeeds, it clarifies intent; when it fails, it prompts caution. This routine reinforces autonomy while supporting informed communication.
Conclusion
In assessing trusted callers, the framework emphasizes verifiable identity, transparent logs, and corroborated context over intuition. Built-in tools for verification, when properly used, reduce uncertainty and reinforce responsible engagement. Red flags—pressure, urgency, and bypassed checks—signal risk. A daily verification routine standardizes timing cues and augments autonomy. Notably, studies show organizations that log verification steps experience 30% fewer successful social engineering attempts, underscoring that disciplined, measurable practices outperform intuition in safeguarding communications.



